An enormous JavaScript-based Node Bundle Supervisor (npm) supply-chain assault has infiltrated code libraries linked to the Ethereum Identify Service (ENS) and lots of of older software program packages, with over 10 broadly used throughout the crypto ecosystem, based on cybersecurity agency Aikido Safety.
Charlie Eriksen, a malware researcher on the safety agency, disclosed that the supply-chain malware often known as “Shai-Hulud: The Second Coming” has contaminated lots of of packages and greater than 25,000 GitHub repositories.
In accordance with the findings, menace actors have embedded this malicious code into over 490 npm packages with greater than 132 million month-to-month downloads, together with outstanding ones from ENS, Zapier, AsyncAPI, Browserbase, and Postman.
Shai-Hulud 2.0: A brand new wave of npm supply-chain assaults focusing on main packages (Zapier, ENS, PostHog, Postman & extra) is ongoing.
Attackers inject malicious code into printed variations, triggering throughout pre-install to achieve code execution and exfiltrate atmosphere vars,…— Charles Guillemet (@P3b7_) November 24, 2025
“If a developer installs one among these unhealthy packages, the malware quietly runs throughout set up, earlier than something even finishes putting in,” Eriksen stated.
How the Shai-Hulud Provide-Chain Malware Works
As described by Akido safety, the Shai-Hulud malware features entry to the developer’s machine or cloud atmosphere throughout set up.
It then deploys an automatic software known as TruffleHog to scan for delicate knowledge, together with passwords, API keys, cloud tokens, and GitHub or NPM credentials.
Any found data is then uploaded to a public GitHub repository titled “Shai-Hulud: The Second Coming.”
If the stolen credentials embody entry to code repositories or bundle registries, attackers can leverage them to breach further accounts and distribute extra malicious packages, permitting the assault to propagate additional.
Evolution from September’s Assault
The preliminary Shai-Hulud breach occurred in early September, marking the biggest npm assault on file on the time, with hackers stealing $50 million in cryptocurrency.
Ledger {hardware} pockets famous that this primary assault was adopted by the Shai Hulud worm spreading autonomously every week later.
Nonetheless, the infiltration technique for this second wave seems considerably completely different.
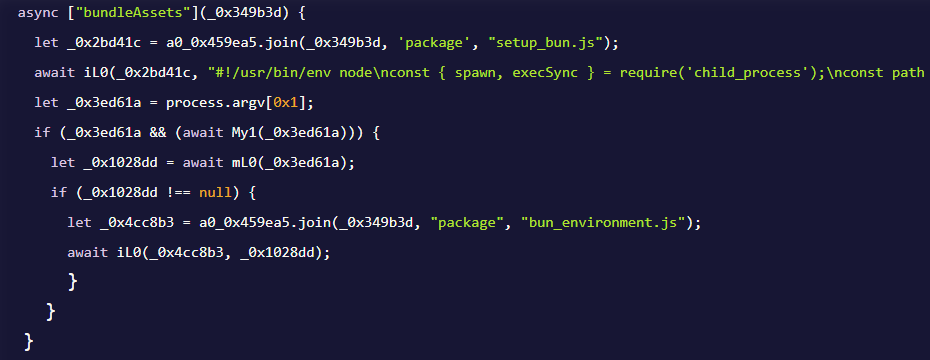
The “Shai-Hulud: The Second Coming” first installs Bun by way of the file setup_bun.js, then makes use of it to execute bun_environment.js, which incorporates the precise malicious code.
It creates randomly named repositories with stolen knowledge fairly than utilizing hardcoded names, and might infect as much as 100 npm packages in comparison with 20 within the earlier assault.
Self-Propagating Malware Exposes Blind Spot in NPM Packages
Charles Guillemet, Chief Know-how Officer at crypto {hardware} pockets Ledger, alerted the group that the malware additionally targets API keys, Git credentials, and CI/CD secrets and techniques, then quietly exfiltrates the whole lot.
“When you use affected packages: PLEASE test this fastidiously: take into account your credentials and secrets and techniques compromised, audit your infrastructure, and rotate your credentials,” he cautioned.
Ledger CTO warned to "AVOID ON-CHAIN TRANSACTIONS" after a JavaScript provide chain assault compromised NPM packages with over 1B downloads. #JavaScript #crypto https://t.co/JjT23tk8CG
— Cryptonews.com (@cryptonews) September 8, 2025
He urged that anybody with out shut CI monitoring would possibly take into account shutting down their techniques.
Florian Roth, Head of Analysis at Nextron Programs, additionally added that it’s turning into more and more straightforward for menace actors to inject malware into delicate techniques as a result of blind spots in NPM packages.
In accordance with his evaluation, the trade beforehand fought malware on the OS stage, however now the identical conduct happens one layer up, contained in the software program ecosystems individuals belief every single day.
We used to battle worms on the OS stage. Slammer, Blaster, Conficker.. all that stuff
Now we get the identical behaviour one layer up – contained in the software program ecosystems we belief every single day
NPM tokens, transitive deps, weak account hygiene, zero visibility… and immediately a… pic.twitter.com/6aSNEL4c32— Florian Roth
(@cyb3rops) November 24, 2025
“NPM tokens, transitive deps, weak account hygiene, zero visibility… and immediately a self-propagating worm runs by way of the availability chain prefer it’s 2003 once more.”
He concluded that the current Shai Hulud breach reveals the actual blind spot is in bundle ecosystems performing as execution surfaces.
“No one screens them, no person hardens them, and attackers don’t even want an exploit to make them go wild,” he stated.
JP Richardson, CEO of Exodus, the primary public firm within the U.S. to tokenize shares on the blockchain, additionally questioned Microsoft for making it “straightforward” for menace actors to propagate malware.
In a November 24 submit, Richardson stated, “What I don’t perceive [is] why Microsoft (npm proprietor) will not be shifting quick sufficient to detect these assaults.”
He believes any bundle that has a pre-install or post-install script added ought to show warnings to everybody on the npm web site and earlier than bundle set up.
The submit Large NPM Provide-Chain Assault Targets ENS-Linked Libraries in Shai Hulud Breach appeared first on Cryptonews.

Leave a Reply